Summary
Technology due diligence catches deal-threatening risks that financial and legal reviews miss. The five most costly:
- End-of-life infrastructure requiring immediate capital outlay
- Cybersecurity gaps that transfer breach liability
- Security incidents revealing deeper maturity problems
- Software licensing hiding audit exposure
- Scalability limitations that prevent growth thesis execution
Download our free 40-point checklist to evaluate these risks in your next acquisition.
Why Technology Diligence Matters
Deal teams examine financials with forensic precision. Legal gets months of scrutiny. But technology—the operational backbone of nearly every portfolio company—often gets reduced to two line items: “IT spend” and “any major issues?”
That leaves money on the table and risk on the books.
According to Bain & Company, 80% of technology due diligence now includes cybersecurity assessment. Yet most mid-market deals still lack a structured IT evaluation framework. We’ve seen it firsthand: a $140K infrastructure requirement, unknown to both buyer and seller until IT assessment, that required a direct adjustment to the offer price before close.
What Infrastructure Problems Do PE Firms Miss at End of Life?
Servers, operating systems, or applications no longer supported by their vendor—Windows Server 2012 or earlier, SQL Server 2012, legacy ERP systems on deprecated platforms. End-of-life means the vendor stopped issuing security patches. Every day these systems run, they accumulate exploitable vulnerabilities.
Deal teams miss it because IT environments look fine from the outside. Systems run, users don’t complain. Financial diligence sees stable IT spend. What it doesn’t see is the deferred capital expenditure behind that number.
The financial impact: Depending on complexity, replacing end-of-life infrastructure post-close can costs upwards of $200k to $3 million—before accounting for business disruption during migration. A full hardware refresh for a 50–200 employee company runs $100K–$500K. These are costs that belong in the deal model, not as post-close surprises.
How Do Cybersecurity Gaps Transfer Breach Liability to Buyers?
No endpoint detection and response (EDR), no multi-factor authentication (MFA) on admin accounts, critical vulnerabilities unpatched for 60+ days, no documented incident response plan. The average data breach costs $4.4 million (IBM 2025)—and pre-acquisition vulnerabilities become the buyer’s liability on day one.
The target says “we have antivirus” and the box gets checked. But consumer-grade antivirus is fundamentally different from managed EDR with 24/7 monitoring—the gap is the difference between detecting an attack in progress and discovering it weeks later. Microsoft’s data shows MFA blocks 99.9% of automated credential attacks, yet we regularly find admin accounts protected by passwords alone.
The financial impact: EDR costs $15–$40 per endpoint/month. MFA costs $3–$6 per user/month. Modest investments compared to average ransomware remediation of $1.85 million. The more immediate deal risk: cyber insurance carriers now require MFA, EDR, and incident response plans for coverage. A target without these controls may be uninsurable.
Download Our Free Checklist: 40-Point IT Due Diligence Assessment for PE Acquisitions
How Can Past Security Incidents Predict Future Risk?
Ask the target about security incidents. They may reluctantly admit they had a ransomware attack two years ago. They paid the ransom, restored operations, and moved on.
But did they conduct root cause analysis? Remediate the vulnerabilities that allowed the breach? Implement the security controls recommended by their insurance carrier? Or did they simply restore from backup and hope it doesn’t happen again?
Security incidents themselves aren’t always deal-breakers, but how the company responded tells you everything about their security maturity. Targets rarely ever volunteer incident history, and standard diligence questionnaires rarely dig into past events.
Compliance gaps compound the risk. A manufacturing target bidding on defense contracts may need CMMC certification that doesn’t exist. A healthcare acquisition may have HIPAA gaps that survived years without an audit. Missing certifications don’t just mean fines—they block customer acquisition. Enterprise buyers increasingly require SOC 2 from vendors, directly constraining growth.
The financial impact: GDPR fines can reach 4% of global revenue. HIPAA violations can reach $50,000 per incident. Compliance remediation runs $50K–$300K depending on certification. The SEC’s increasing focus on cybersecurity practices for registered investment advisers signals broader regulatory expectations around cyber risk management—including how firms evaluate targets during diligence.
What Software Licensing Risks Create Compliance Exposure?
No centralized software inventory, licenses that don’t match usage, auto-renewing contracts nobody reviews, and SaaS subscriptions procured by departments without IT oversight. Conduct a license audit and you may discover the target is using 400 licenses but only paying for 200.
A licensing audit triggered post-acquisition by a firm that conducts active audit programs (like Microsoft, Oracle, or Adobe) can produce six- to seven-figure true-up costs with limited negotiating leverage.
The financial impact: Software licensing represents 15–30% of IT budget. Consolidation routinely saves 20–40%—a value creation opportunity when managed proactively and a financial surprise when discovered reactively. Consolidating software across your portfolio companies creates additional negotiating leverage through volume pricing.
Can the Technology Scale to Support Your Growth Thesis?
Your investment thesis projects 3x growth. But can the technology infrastructure support it? Many mid-market companies build systems that work at current scale but break under growth. Like when a database that handles 1,000 transactions per day starts timing out at 3,000.
5 scalability issues that derail growth plans:
- Database architecture limitations: Legacy databases that can’t be sharded or distributed
- Manual processes disguised as workflows: “The system generates reports, but Susan manually consolidates them in Excel”
- Single-tenant infrastructure: Adding users requires linear cost increases
- Key-person dependencies: Entire IT function relies on one person with no documentation or succession plan
- Geographic constraints: System architecture tied to a single data center or region
Current-state performance masks future-state limitations. Key-person IT dependencies are invisible until that person leaves—which ownership transitions frequently trigger.
The financial impact: Knowledge documentation and transition projects run $50K–$150K. Scalability remediation ranges from infrastructure upgrades ($100K–$500K) to full application rewrites ($500K–$2M+), with 12–18 months of implementation time.
What PE Firms Should Do Differently
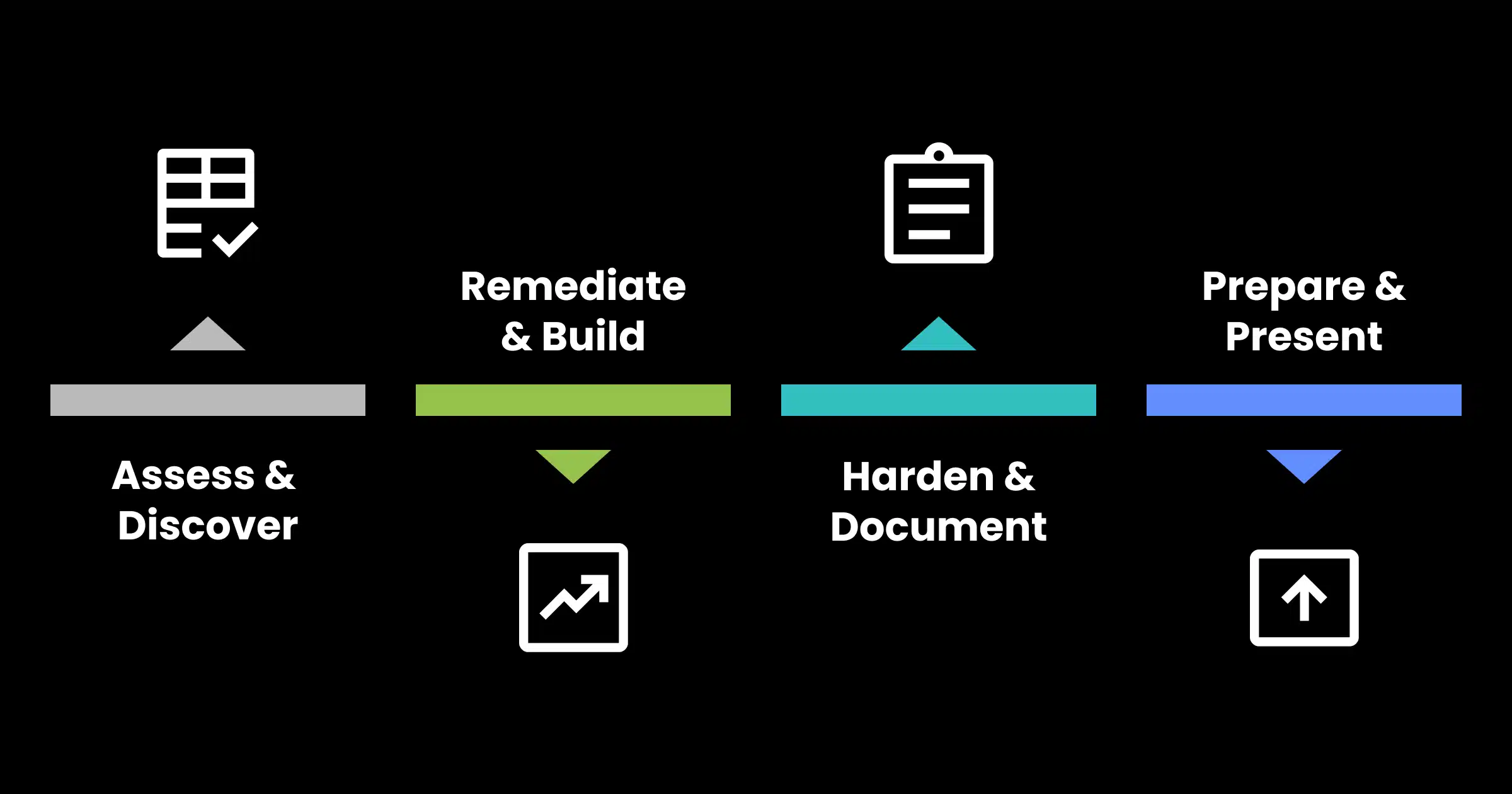
The firms that extract maximum value integrate technology assessment throughout the deal process:
Pre-LOI (3–5 days): High-level tech stack review to identify deal-killers or material valuation impacts.
Post-LOI (2–3 weeks): Comprehensive assessment across infrastructure, cybersecurity, technical debt, software licensing, data management, and IT organization. Quantify remediation costs, identify value creation opportunities, and build your 90-day post-close roadmap.
Pre-Close (3–5 days): Final verification that no material changes have occurred.
The deliverable shouldn’t be an academic report. Practical technology due diligence translates technical findings into business impact: “The ERP system is at end of life” becomes “Expect $2 million to replace and 18 months to implement, delaying integration by one quarter.”
Start with the checklist. Our 40-point IT Due Diligence Checklist gives your deal team a structured framework for evaluating technology risk before surprises surface post-close.
Download our free 40-point checklist to evaluate these risks in your next acquisition.
Frequently Asked Questions
When should IT due diligence happen?
During confirmatory diligence, alongside financial and legal. A 3–5 day pre-LOI review can identify deal-breakers before significant expense is committed.
How long does a technology assessment take?
2–4 weeks for a mid-market company.
Should the target’s IT team conduct the assessment?
No. Independent third-party assessment provides objectivity and benchmarking the target’s team can’t deliver.
How does IT diligence differ for platform vs. add-on acquisitions?
Platform acquisitions require deeper assessment—you’re establishing the IT foundation. Add-ons focus on integration readiness and cost.
What IT risks most commonly affect valuation?
End-of-life infrastructure, cybersecurity vulnerabilities increasing insurance costs, licensing non-compliance, and scalability limitations. All quantifiable and negotiable when identified during diligence.
About Arakÿta
Since 2002, Arakÿta has provided managed IT services, cybersecurity, and strategic technology consulting to mid-market companies. Through our partnership with OceanView Operating Partners (announced 2025), we deliver IT due diligence, post-acquisition integration, and fractional vCIO support built for private equity firms and their portfolio companies nationwide.
Ready to strengthen your technology due diligence? Contact Arakÿta to discuss how we can support your next acquisition.
Contact Arakÿta: Phone: 419-740-7150 | arakyta.com
References & Resources
IBM Cost of a Data Breach Report 2025
Bain & Company – Technology Due Diligence in Private Equity
Microsoft – Multi-Factor Authentication Statistics Verizon Data Breach
Verizon Data Breach Investigations Report (DBIR)
Arakÿta – Arakÿta and OceanView Announce Strategic Partnership