Summary
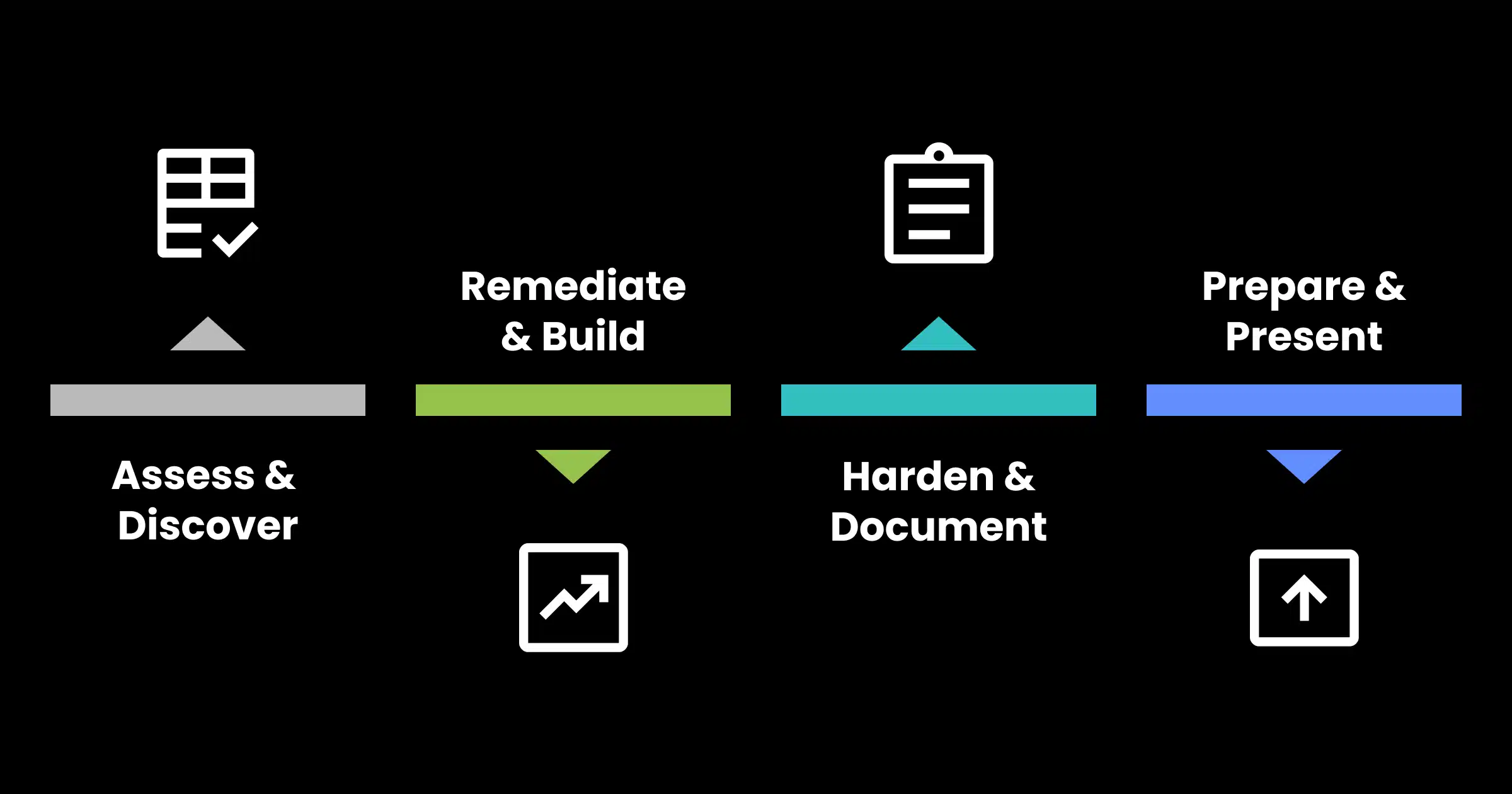
Technology readiness affects exit valuation more than most PE firms expect. Buyers are doing deeper IT due diligence than ever — and what they find (or don’t find) can move multiples. This 12-month playbook walks portfolio company leaders through assessment, standardization, documentation, and audit readiness so technology becomes a value driver, not a deal risk.
Table of Contents
- Why Technology Readiness Defines Exit Outcomes
- Months 12–10: Assessment & Foundation
- Months 9–7: Standardization & Documentation
- Months 6–4: Optimization & Visibility
- Months 3–0: Audit Readiness & Value Demonstration
- The 5 IT Issues That Kill Deals at the Finish Line
- Frequently Asked Questions
Turn Technology Into a Value Creation Story
Buyers conduct their own IT due diligence and what they find moves multiples. The 12-Month IT Exit Prep Playbook maps every action — assessment, remediation, documentation, and audit readiness — to a timeline that ends with a buyer-ready IT environment and a clean diligence process.
Why Technology Readiness Defines Exit Outcomes
If it’s not a strategic focus, most PE firms would spend the last 90 days before LOI scrambling to clean up IT.
That’s 90 days too late.
Buyers aren’t just kicking tires on financials anymore. Technology due diligence has become a standard part of the acquisition process. And, buyers know exactly what to look for:
- Undocumented systems
- Licensing gaps
- Technical debt
- Security posture that doesn’t match the company’s revenue profile
What they find moves multiples.
A portfolio company with clean, documented, scalable IT infrastructure signals operational maturity. It tells buyers the business is ready to absorb integration and grow. A company with spaghetti infrastructure and a reactive IT function tells a different story. A story that justifies a haircut.
The difference between those two outcomes isn’t talent or luck. It’s preparation time.
Start 12 months out. Here’s how.
Months 12–10: Assessment & Foundation
Conduct a Full IT Infrastructure Audit
You can’t fix what you haven’t mapped. Month one starts with a comprehensive audit of every system, vendor contract, software license, and piece of hardware in the portfolio company’s environment.
What this covers:
- Network architecture and connectivity
- Server infrastructure (on-premise and cloud)
- End-user device inventory and lifecycle status
- All SaaS and licensed software with contract terms and renewal dates
- Active vendor relationships and MSP agreements
- Backup and disaster recovery configurations
- Current security posture (firewalls, endpoint protection, patch cadence)
The goal isn’t to judge. It’s to create a complete picture. Gaps and risks identified here become your roadmap for the next nine months.
Identify and Prioritize Risk
Not every IT issue carries the same exit risk. Some findings are cosmetic and can be easily explained or remediated during diligence. Others are deal-stoppers.
High-risk findings typically fall into three categories:
- Security vulnerabilities | Unpatched systems, missing MFA, inadequate endpoint protection
- Compliance gaps | Industry-specific requirements not met (HIPAA, SOC 2, CMMC, SEC regulations)
- Documentation voids | No runbooks, no system inventories, no IT policies on paper
Prioritize remediation in that order. A buyer’s security consultant will find the vulnerabilities. Your job is to find them first.
Establish Baseline KPIs
What gets measured gets managed. And what gets managed gets credited at exit. Establish baseline technology KPIs now so you can show improvement over the 12-month timeline.
Key metrics to track:
- System uptime and availability
- Mean time to resolve (MTTR) for IT incidents
- Patch compliance rate (target: 95%+ within 30 days of release)
- Security incident frequency and severity
- Help desk ticket volume and resolution time
- IT spend as a percentage of revenue
These numbers tell a story. By the time you exit, you want that story to be one of consistent improvement.
Months 9–7: Standardization & Documentation
Standardize the Technology Stack
Buyers struggle to integrate acquisitions with fragmented technology environments. The more standardized your stack, the lower the perceived integration risk — and integration risk gets priced into deals.
Standardization priorities:
- Consolidate to a single endpoint management platform
- Standardize email and collaboration tools (Microsoft 365 or Google Workspace – pick one)
- Establish a uniform identity management approach (Active Directory or equivalent)
- Consolidate overlapping SaaS tools. Most portfolio companies are running 3-5x the software they actually need
- Move workloads to cloud infrastructure where it makes operational and cost sense
This isn’t about perfection. It’s about reducing the complexity a buyer will inherit.
Build the Documentation Library
Here’s the thing about documentation: buyers don’t just want to see that your systems work. They want to see that someone knows how they work and has written it down.
The documentation every portfolio company needs before exit:
- Network topology diagrams (current state)
- System runbooks for all critical applications
- IT policies (acceptable use, password policy, incident response, data classification)
- Vendor and contract register with renewal dates and termination terms
- Business continuity and disaster recovery plan (tested, not theoretical)
- Security incident log (clean history is good; documented response to incidents is better)
- User access review records (who has access to what, and when it was last reviewed)
If it’s not documented, a buyer’s diligence team will assume it doesn’t exist.
Months 6–4: Optimization & Visibility
Optimize IT Spend
Technology cost optimization accomplishes two things: it improves EBITDA (directly affecting valuation multiples) and it demonstrates operational discipline to buyers.
Where to look:
- Software licensing | Most companies are overpaying for seats they’re not using
- Cloud infrastructure | Right-size compute and storage to actual utilization
- Vendor contracts | Consolidate where possible, renegotiate where you can’t
- Managed service agreements | Ensure scope matches current needs
A 10-15% reduction in IT spend doesn’t just improve the P&L. It signals that IT is being managed, not just administered.
Implement Security Controls That Show
Buyers will ask about cybersecurity. Specifically, they’ll want to know what controls are in place, whether they’ve been tested, and whether the company has had any incidents.
The security controls that generate the most due diligence credit:
- Multi-factor authentication (MFA) | deployed across all users, including executives
- Endpoint Detection and Response (EDR) | not just antivirus
- Email security controls | SPF, DKIM, DMARC properly configured
- Privileged access management | limiting who has admin rights and logging what they do with them
- Security awareness training | documented program with completion records
- Penetration test or vulnerability assessment | conducted within the past 12 months
Having a recent pen test with a clean (or remediated) report is worth more than any sales pitch about your security posture.
Make IT Visible to the Business
One of the most underestimated exit preparation moves is elevating how IT is represented at the leadership level. When IT operates as a silent function, buyers assume it’s reactive and under managed.
Practical steps:
- Establish a monthly IT steering committee with leadership visibility
- Create a technology roadmap that aligns with business growth objectives
- Present IT KPIs alongside operational and financial metrics in board reporting
- Document the technology strategy — where you are, where you’re going, why
This is exactly where a virtual CIO (vCIO) delivers disproportionate value. A vCIO provides the strategic IT leadership and documentation that PE buyers expect without the cost and overhead of a full-time C-suite hire.
Months 3–0: Audit Readiness & Value Demonstration
Conduct a Pre-Sale IT Assessment
Three months before you expect to be in market, run a mock IT due diligence exercise. Hire a third party to review your environment the way a buyer’s consultant will.
What to assess:
- Infrastructure readiness and documentation completeness
- Security posture and control effectiveness
- Licensing compliance (software audits surface issues at the worst possible times)
- Vendor contract health (identify any problematic terms, auto-renewals, or change-of-control clauses)
- IT organizational structure and key-person risk
Address findings before they become buyer leverage.
Build the IT Due Diligence Package
Sophisticated sellers don’t wait for buyers to ask questions. They prepare the answers.
Your IT due diligence package should include:
- Executive summary of the technology environment
- Infrastructure overview with architecture diagrams
- Security posture summary with control inventory
- Vendor register and key contract terms
- IT organizational chart and key personnel
- Technology roadmap for the next 12-24 months
- IT spend analysis with benchmarks
- Incident history and response documentation
A well-prepared IT due diligence package accelerates the buyer’s process, reduces uncertainty, and positions technology as an asset — not a liability.
Tell the Technology Story
By exit, you should have 12 months of data showing improvement. Use it.
Uptime improved from 97% to 99.8%. IT spend reduced 14% while capability expanded. Security incident rate dropped by half. A modern, documented, cloud-forward infrastructure replacing a legacy environment that was holding the business back.
That’s not an IT story. That’s a value creation story.
The 5 IT Issues That Kill Deals at the Finish Line
Even well-prepared portfolio companies can get tripped up. Watch for these:
- Undisclosed legacy systems that surface during technical diligence — always disclose, never surprise
- Key-person IT risk — a single person who holds all the institutional knowledge with no documentation
- Software licensing gaps — unlicensed software or over-deployment creates legal exposure buyers won’t accept
- Unremediated security vulnerabilities from a pen test — having a test with open findings is worse than no test
- Change-of-control clauses in vendor contracts — some agreements require renegotiation or termination at exit, affecting continuity
Frequently Asked Questions
When should we start IT exit preparation?
12 months is the target. 18 months is better. 6 months is the minimum to address anything meaningful. If you’re already inside 90 days of a process, focus on documentation and transparency, not remediation theater.
What’s the ROI of IT exit preparation?
It depends on what you find. Addressing a significant compliance gap or security vulnerability before diligence can mean the difference between a clean process and a price reduction. The cost of preparation is almost always a fraction of the cost of discovery.
Do we need a full-time CIO for this?
Not necessarily. A virtual CIO (vCIO) can deliver the strategic leadership, documentation, and executive visibility this process requires at a fraction of the cost. For many mid-market portfolio companies, this is the most efficient path to exit-ready technology leadership.
What’s the biggest mistake PE firms make in IT exit prep?
Starting too late and treating IT preparation as a checkbox rather than a value creation lever. The firms that get this right treat technology readiness the same way they treat financial reporting: as something that affects every conversation at every stage of the exit process.
Ready to build your exit-ready IT foundation? Arakÿta works with PE firms and portfolio companies across the Midwest to develop the technology strategy, documentation, and security posture that buyers expect to see. Download the 12-Month IT Exit Prep Timeline & Playbook or contact us to schedule a technology assessment for your portfolio company.uantifiable and negotiable when identified during diligence.
About Arakÿta
Since 2002, Arakÿta has provided managed IT services, cybersecurity, and strategic technology consulting to mid-market companies. Through our partnership with OceanView Operating Partners (announced 2025), we deliver IT due diligence, post-acquisition integration, and fractional vCIO support built for private equity firms and their portfolio companies nationwide.
Ready to strengthen your technology due diligence? Contact Arakÿta to discuss how we can support your next acquisition.
Contact Arakÿta: Phone: 419-740-7150 | arakyta.com